3.1 KiB
3.1 KiB
David Westgate 31 May 2024
HW7 for gensec
The purpose of this assignment is to generate a security related application using aider. The application I will attempt to generate is a wifi penetration testing python. The intention is that this application will be able to perform the same wifi cracking that my hw6 LLM application did.
Input
Generate a python application to assist in wifi penetration testing by prompting the user for the name (SSID) of a password protected wifi network and returning the plaintext password.
This python application should use a combination of shell tools assumed to be on the users linux system, including but not limited to iwconfig, airmon-ng, airodump-ng, aireplay-ng, aircrack-ng.
Operations may be run sequentially, or in parallel using multi-threading
As needed, the use of shell tools should utilize sudo capabilities
As needed, the application may utilize a wordlist found at ~/rockyou.txt
As needed, the application can change the state of the users wifi interface between managed and monitor mode
Save this to hw7/{llm}/app.py
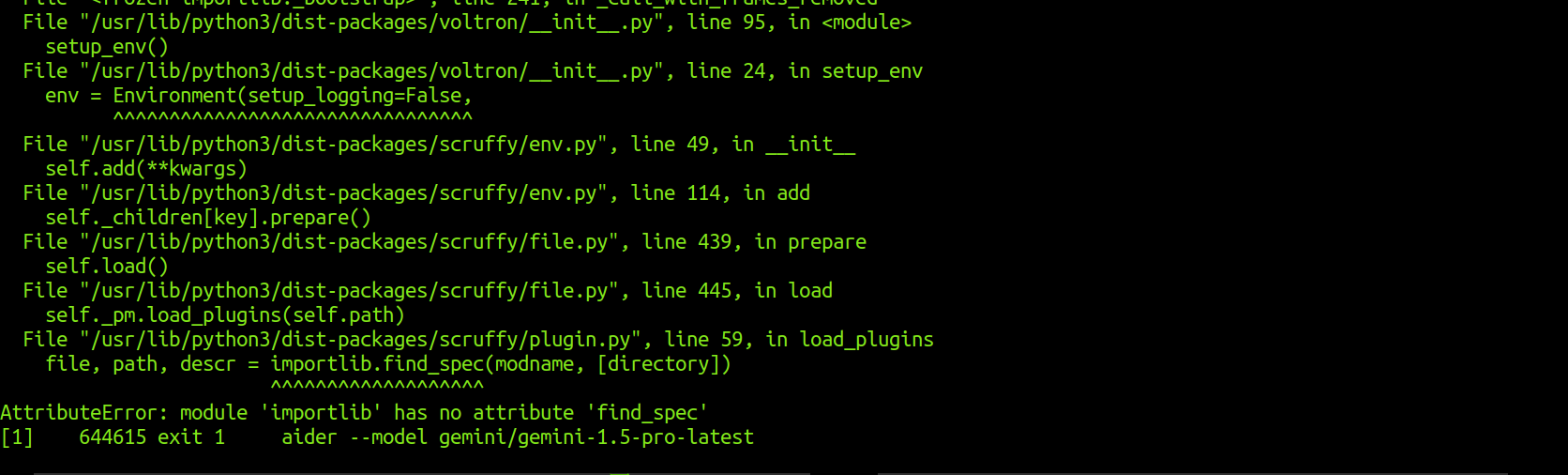
Errors
All runs gave the following python error, but were able to generate code regardless
Results - Gemini (gemini 1.5)
aider --model gemini/gemini-1.5-pro-latest
I was able to get aider to output a program with the gemini LLM
Code output
Test
python3 hw7/gemini/app.py
Results - GPT4 (gpt40)
aider --model openai/gpt-4o
Code output
Test
python3 hw7/gpt4/app.py
Results - Claude (claude-opus)
aider --model claude-3-opus-20240229
I was able to redeem $5 of free API credits for this test
Code output
Along with the code output, claude gave a nice summary
This application does the following:
1 Gets the available WiFi interfaces using iwconfig
2 Prompts the user to enter the SSID of the target network
3 Changes the WiFi interface to monitor mode using airmon-ng
4 Captures the handshake for the target network using airodump-ng and aireplay-ng
5 Changes the WiFi interface back to managed mode
6 Cracks the password using the captured handshake file and a wordlist (~/rockyou.txt) with aircrack-ng
7 Prints out the cracked password for the target network
It uses subprocess to run the shell commands and re to parse the output. The WiFi interface is changed between managed and monitor modes
as needed.
Test
python3 hw7/claude/app.py