3.0 KiB
Homework 3: Cracking WiFI!
For this homework assignment, I will demostrate cracking the NetSec WiFi network, and performing some reconissance. I will do this via the mallory machine, running kali
Crack the NetSec WiFi network password with bettercap
Find the BSSID and connected client of the NetSec Network
Perform a deauth attack on the network with bettercap and capture the 4-way handshake
Use the hcx toolsuite to convert the captured handshake to a format that hashcat can understand
Crack the password using hashcat and rockyou.txt
Connect workstation to the wifi network and show using nmtui
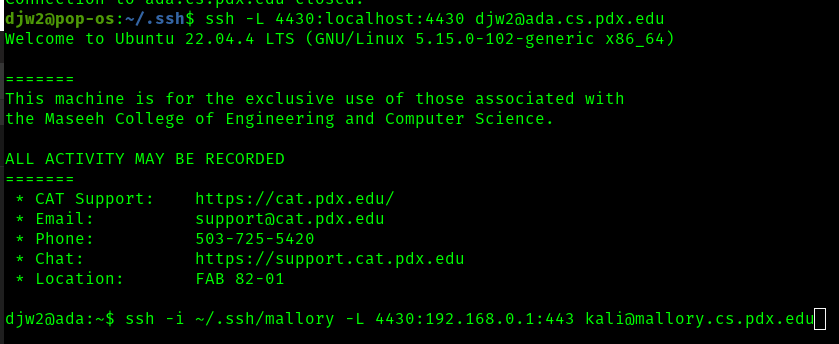
Now that I have found the password, I can initiate a wifi connection from mallory to the raspberry pi
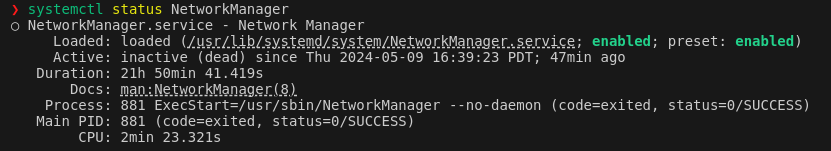
The first issue encountered was the the network manager was inactive. This is confirmed by running systemctl status NetworkManager
This was fixed by running sudo systemctl start NetworkManager
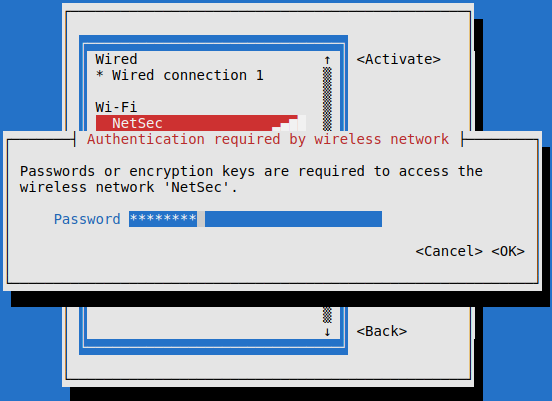
Now with sudo nmtui I can finally attempt connect to NetSec with the password, crackme1.
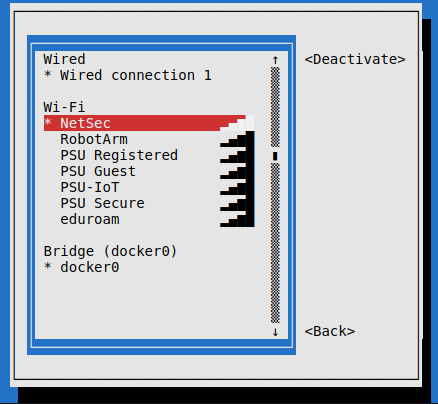
The connection was successfull
Scan the network with nmap
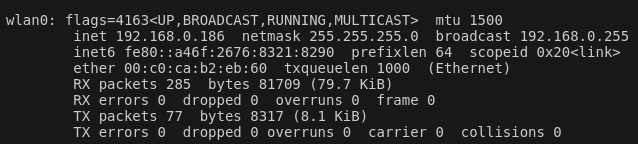
I now want to scan the network to identify the router, and devices connected to the router. A quick check with iwconfig and looking at the wlan0 interface shows that as a client of this router, we are in the subnet 192.168.0.0/24
Now running sudo nmap -sn 192.168.0.0/24 (a simple ping scan) we have some interesting results. I've run this a few times on different days to see which hosts are persistant, and less likely to be other students
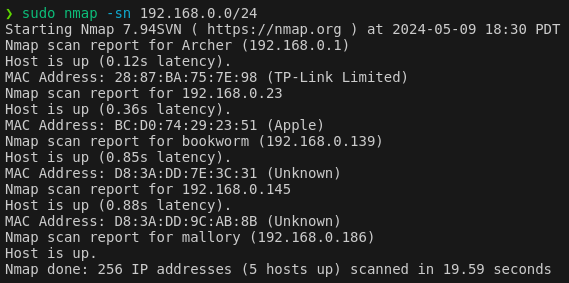
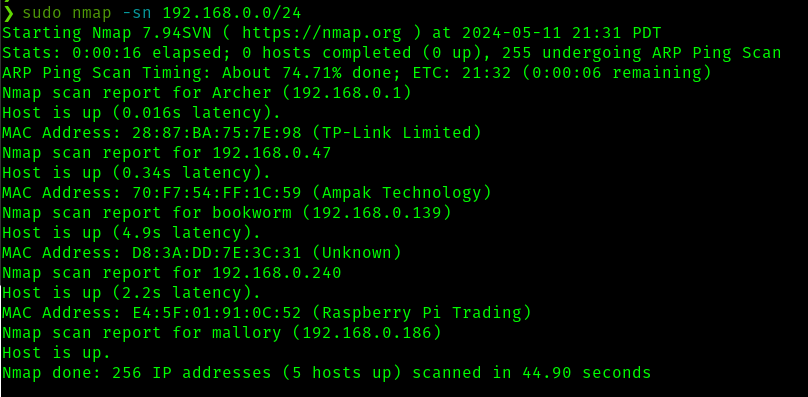
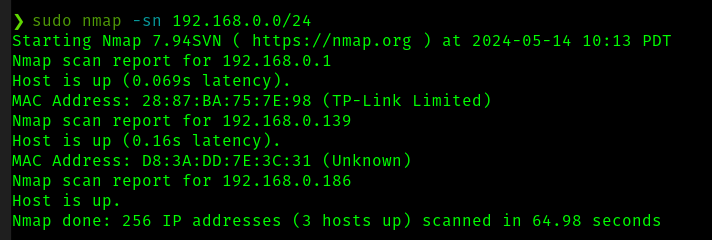
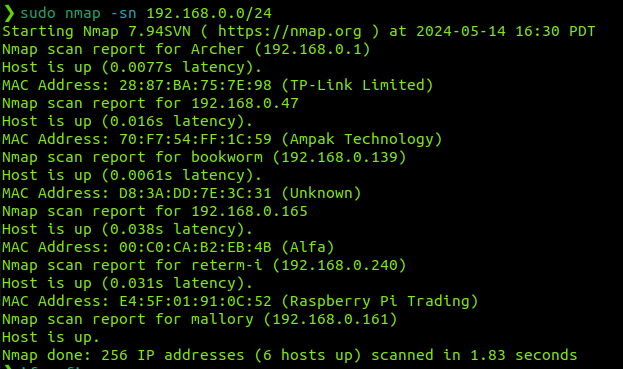
To summerize this, the interesting devices, excluding ourselves (mallory) are
Nmap scan report for Archer (192.168.0.1)
MAC Address: 28:87:BA:75:7E:98 (TP-Link Limited)
Nmap scan report for bookworm (192.168.0.139)
MAC Address: D8:3A:DD:7E:3C:31 (Unknown)
We have one router/gateway (archer/28:87:BA:75:7E:98), one persistant client device (bookworm/D8:3A:DD:7E:3C:31). The other devices shown in some of these scans do not seem to persist and are not shown in my last scan which is at the time of writing. I will now scan for open ports on these available devices.
Open ports and services on archer
As the router/gateway, I do not expect any interesting servcies to be running here. But let us make sure
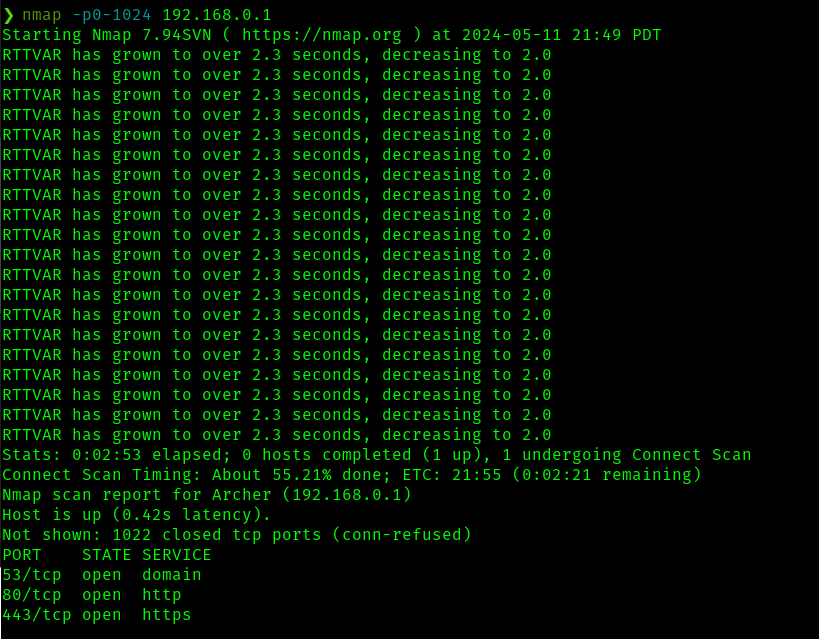
As probably expected, our gateway is responding to DNS requests, and has a web interface open on http(s).
Let's assume the port 80 traffic is only allowed to redirect users to the SSL web traffic on 443. From my home machine, I can do the following to tunnel traffic and take a look at the web page