10 KiB
Homework 4: Find the firmware
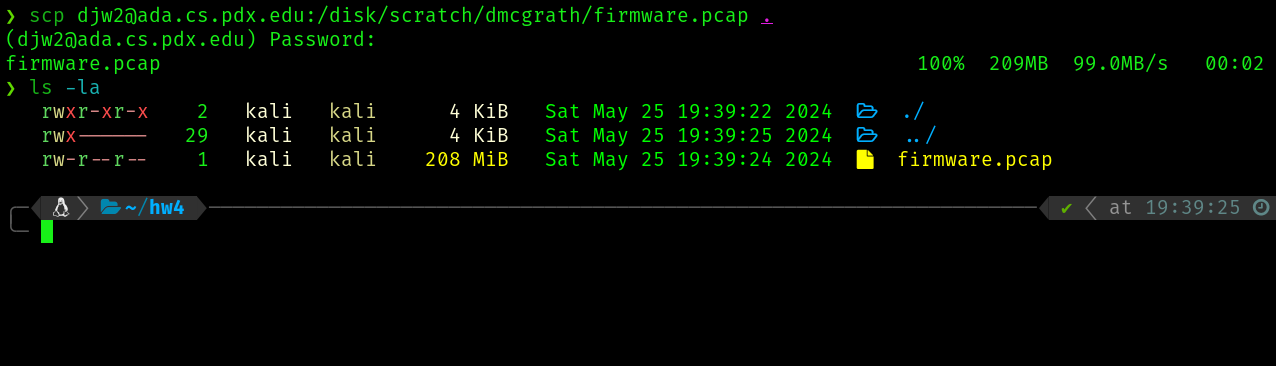
We start by copying the firmware capture file from ada to our machine
Reverse Engineering
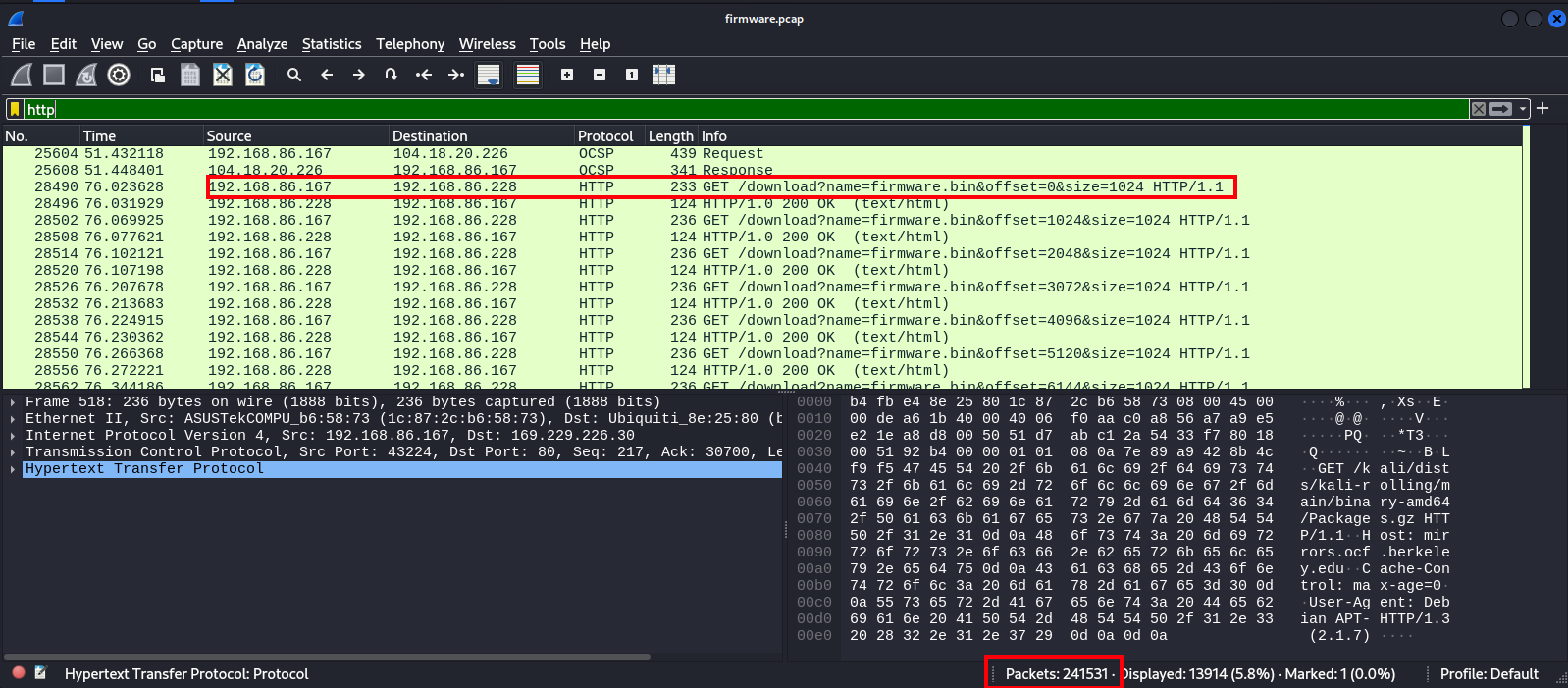
First lets open this capture up in wireshark and do a high level overview
Wireshark overview
Knowing we are ultimetly looking to re-construct a firmware download, we can discern some important info from wireshark
- There are 241,531 packets in this capture, but only some are the traffic directly related to this download
- Client of the download is 192.168.86.167 and server origin is 192.168.86.228:5000
- The download is split over multiple HTTP requests by the shown convention, which themselves are split over multiple TCP requests
A starting point of a BPF might look like tcp and src host 192.168.86.228 and src port 5000 and dst host 192.168.86.167
As a wireshark filter, this would be tcp && ip.src == 192.168.86.228 && tcp.srcport == 5000 && ip.dst == 192.168.86.167
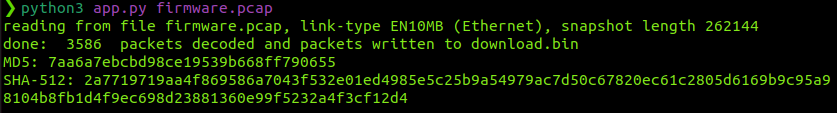
Scapy
I wrote a python scapy script will help us work with this capture file to assemble the .bin from the raw response of the relevant TCP packets. This script is shown in ./app.py. Our script will confirm the extracted binary matches the following checksums
MD5: 7aa6a7ebcbd98ce19539b668ff790655
SHA256: 2a7719719aa4f869586a7043f532e01ed4985e5c25b9a54979ac7d50c67820ec61c2805d6169b9c95a98104b8fb1d4f9ec698d23881360e99f5232a4f3cf12d4
When writing this script I had to dig deeper into the packet capture to understand how the content was being transmitted. As it turns out, in the interesting response packets noted above, base64 encoded data was contained accross a pair of TCP responses for every HTTP request in the session. The first packet of this pair contained content after \r\n\r bytes were appear in the raw data. The second packet of the pair was the immediete next packet in the TCP session, and all of its raw data comprised the rest of this chunk. I wrote a loop on the filtered packet list which was able to extract and compound the overall payload with this technique. As we see, we produce a download.bin with the proper hash and we can move on to exploring it
Running binwalk -M -e download.bin, we can extract the underlying linux filesystem of this binary
djw2@pop-os:~/Documents/netsec/netsec-djw2/hw4$ binwalk -M -e download.bin
Scan Time: 2024-06-01 17:24:53
Target File: /home/djw2/Documents/netsec/netsec-djw2/hw4/download.bin
MD5 Checksum: 7aa6a7ebcbd98ce19539b668ff790655
Signatures: 411
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
48 0x30 Unix path: /dev/mtdblock/2
96 0x60 LZMA compressed data, properties: 0x6D, dictionary size: 8388608 bytes, uncompressed size: 4438276 bytes
302958 0x49F6E MySQL MISAM index file Version 4
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/etc/localtime -> /tmp/localtime; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/etc/TZ -> /tmp/TZ; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/etc/resolv.conf -> /tmp/resolv.conf; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/etc/mtab -> /proc/42002/mounts; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/etc/ppp/resolv.conf -> /tmp/resolv.conf.ppp; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/sbin/ip -> /usr/bin/busybox; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/usr/bin/pgrep -> /usr/bin/busybox; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/usr/bin/flock -> /usr/bin/busybox; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/usr/bin/uptime -> /usr/bin/busybox; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/usr/bin/free -> /usr/bin/busybox; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/usr/bin/ssh -> /usr/sbin/dropbear; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/usr/bin/top -> /usr/bin/busybox; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/usr/bin/scp -> /usr/sbin/dropbear; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/bin/ps -> /usr/bin/busybox; changing link target to /dev/null for security purposes.
WARNING: Symlink points outside of the extraction directory: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/squashfs-root/bin/kill -> /usr/bin/busybox; changing link target to /dev/null for security purposes.
1441888 0x160060 Squashfs filesystem, little endian, version 4.0, compression:xz, size: 2208988 bytes, 1159 inodes, blocksize: 262144 bytes, created: 2019-08-06 21:20:37
Scan Time: 2024-06-01 17:24:53
Target File: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/60
MD5 Checksum: 24d29d1dc329ae3314c4899a5e41fe83
Signatures: 411
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
1040 0x410 Flattened device tree, size: 4729 bytes, version: 17
3708304 0x389590 CRC32 polynomial table, little endian
3734583 0x38FC37 Intel x86 or x64 microcode, sig 0x03000000, pf_mask 0x01, 2088-18-20, rev 0x3baa3000, size 136
3869788 0x3B0C5C xz compressed data
3902428 0x3B8BDC Unix path: /lib/firmware/updates/4.14.95
3921700 0x3BD724 Unix path: /sys/firmware/devicetree/base
3922521 0x3BDA59 Unix path: /sys/firmware/fdt': CRC check failed
3931117 0x3BFBED Neighborly text, "neighbor table overflow!solicit"
3950660 0x3C4844 Neighborly text, "NeighborSolicitsports"
3950680 0x3C4858 Neighborly text, "NeighborAdvertisements"
3953602 0x3C53C2 Neighborly text, "neighbor %.2x%.2x.%pM lost rename link %s to %s"
4280320 0x415000 ELF, 32-bit LSB MIPS64 shared object, MIPS, version 1 (SYSV)
4437760 0x43B700 ASCII cpio archive (SVR4 with no CRC), file name: "dev", file name length: "0x00000004", file size: "0x00000000"
4437876 0x43B774 ASCII cpio archive (SVR4 with no CRC), file name: "dev/console", file name length: "0x0000000C", file size: "0x00000000"
4438000 0x43B7F0 ASCII cpio archive (SVR4 with no CRC), file name: "root", file name length: "0x00000005", file size: "0x00000000"
4438116 0x43B864 ASCII cpio archive (SVR4 with no CRC), file name: "TRAILER!!!", file name length: "0x0000000B", file size: "0x00000000"
Scan Time: 2024-06-01 17:24:54
Target File: /home/djw2/Documents/netsec/netsec-djw2/hw4/_download.bin.extracted/_60.extracted/console
MD5 Checksum: d41d8cd98f00b204e9800998ecf8427e
Signatures: 411
DECIMAL HEXADECIMAL DESCRIPTION
--------------------------------------------------------------------------------
Questions
- What architecture is the firmware intended to run on?
The architecture appears to be MIPS 32-bit. This is shown by running file on the busybox binary

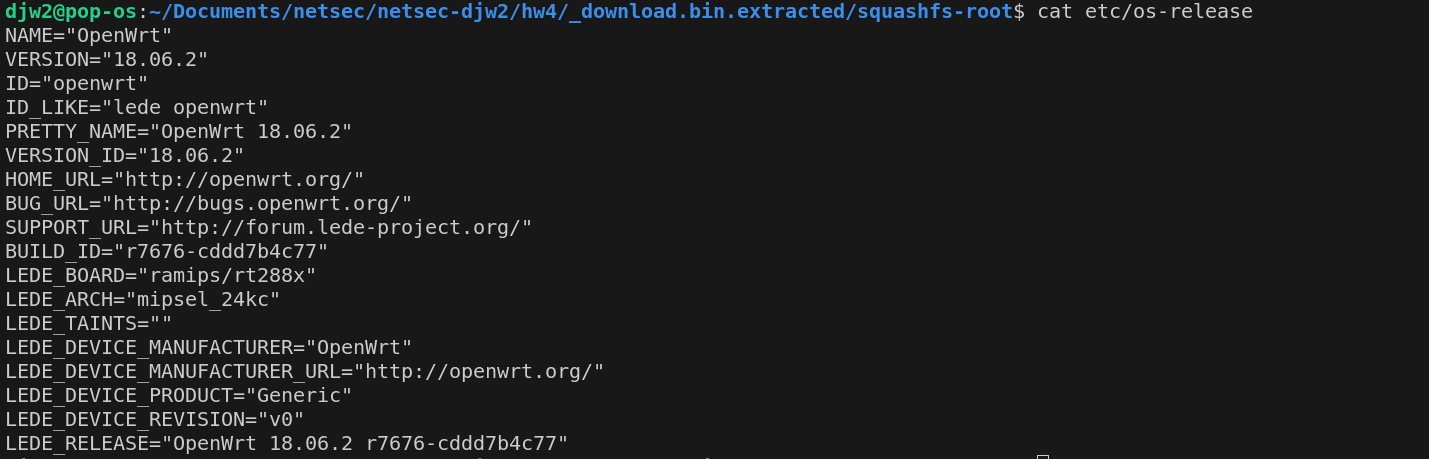
- What OS is the firmware running?
As shown in etc/os-release, the OS appears to be OpenWRT
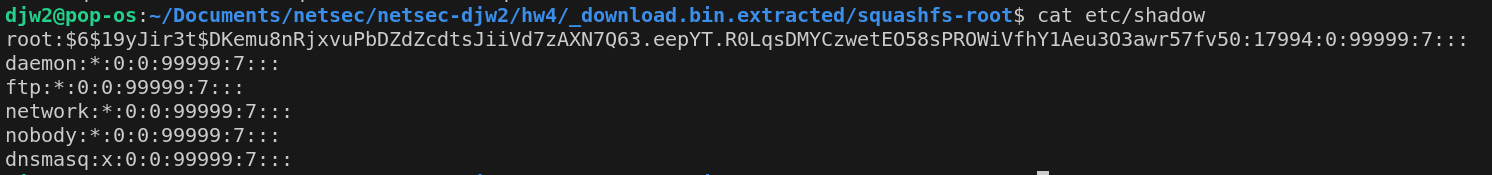
- What users are present on the system?
root, daemon, ftp, network, nobody, and dnsmasq are the users present (seen in /etc/shadow and /etc/passwd)
- What is the root password?
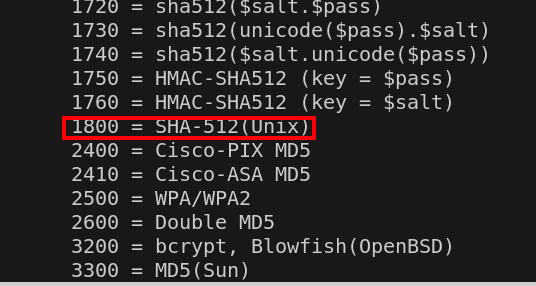
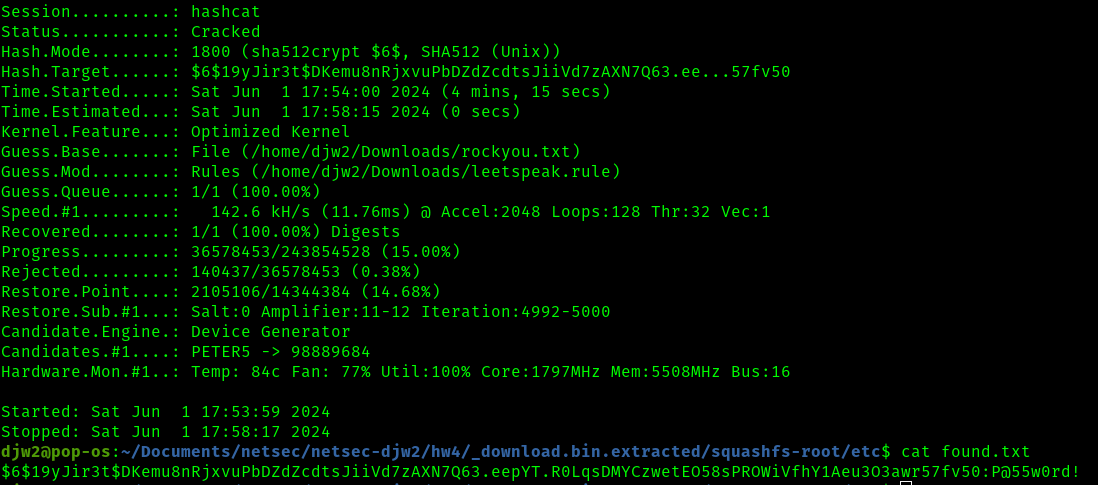
The hash of the root password shown above is as follows
root:$6$19yJir3t$DKemu8nRjxvuPbDZdZcdtsJiiVd7zAXN7Q63.eepYT.R0LqsDMYCzwetEO58sPROWiVfhY1Aeu3O3awr57fv50:17994:0:99999:7:::
$6 indicated a sha512 hash and the next chunk 19yJir3t indicates the salt.
For sha512, we will want to use -m 1800 flag with hashcat
I then tried to crack the password hashcat and rockyou.txt, but was unable to find the password. Some quick googling revealed the leetspeak.rule wordlist in combination with rockyou.txt might be a good choice (as well as the page which simply gave us the password for this exercise)
For fun, I'll crack the password anyways running hashcat -O -m 1800 -a 0 -o found.txt hash.txt ~/Downloads/rockyou.txt -r ~/Downloads/leetspeak.rule
In about 4 minutes with my Nvidia 1080 Ti, we have cracked the password - That being P@55w0rd!